Hacktivists have claimed responsibility for taking down the public-facing infrastructure of popular Linux operating system distribution Ubuntu, as well as Canonical, the company that develops and maintains the software. The attack began on Thursday, and affected services that Ubuntu users rely on.
“Canonical’s web infrastructure is under a sustained, cross-border attack and we are working to address it. We will provide more information in our official channels as soon as we are able to,” the company said on its website.
The hacktivists are believed to have launched a distributed denial-of-service, or DDoS, a crude but often effective attack that consists of flooding a target with junk traffic until it overloads or crashes.
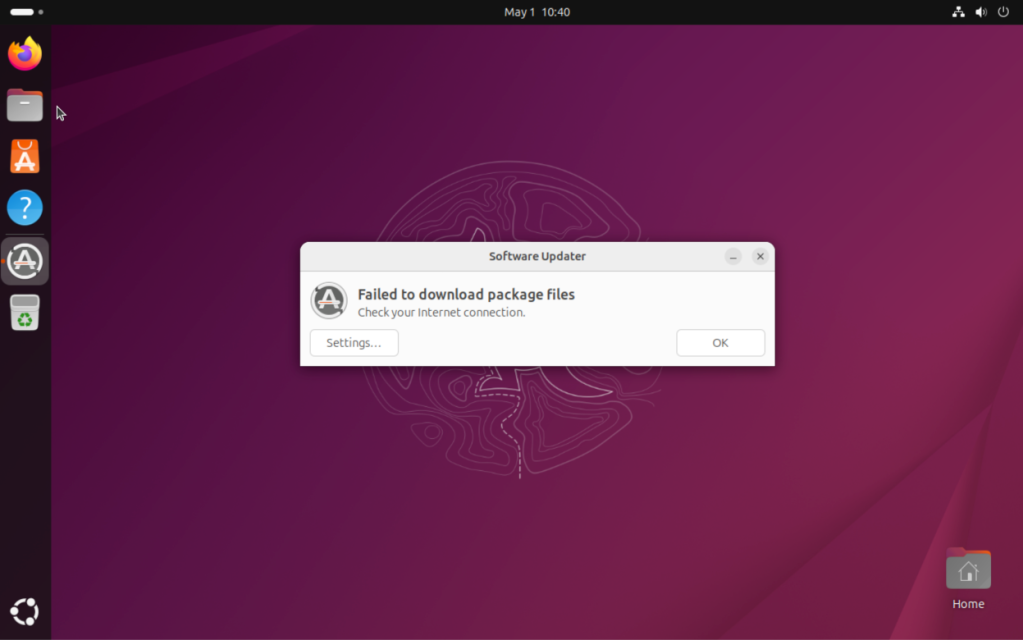
Ubuntu developers have been discussing the attack on an unofficial Ubuntu community forum, claiming that the attack affects Ubuntu’s security API, and several Ubuntu and Canonical websites. According to a post on a threat intelligence forum, the DDoS attack has also made it impossible for users to update and install Ubuntu. TechCrunch verified that updates failed to install on a test device running Ubuntu.
As of this writing, the outage has been ongoing for around 20 hours.
When contacted, Canonical spokesperson Lelanie de Roubaix reiterated what the company said on is website.
Hacktivists calling themselves The Islamic Cyber Resistance in Iraq 313 Team claimed on its Telegram channel that it was to blame for the DDoS attack.
Meet your next investor or portfolio startup at Disrupt
Your next round. Your next hire. Your next breakout opportunity. Find it at TechCrunch Disrupt 2026, where 10,000+ founders, investors, and tech leaders gather for three days of 250+ tactical sessions, powerful introductions, and market-defining innovation. Register now to save up to $410.
Meet your next investor or portfolio startup at Disrupt
Your next round. Your next hire. Your next breakout opportunity. Find it at TechCrunch Disrupt 2026, where 10,000+ founders, investors, and tech leaders gather for three days of 250+ tactical sessions, powerful introductions, and market-defining innovation. Register now to save up to $410.
The hackers claimed to be using Beamed, a DDoS-for-hire service. These types of services, also called booters or stressers, allow anyone to pay to launch DDoS attacks, even if they have no technical skills nor the necessary infrastructure to flood targets with bogus traffic. The DDoS-for-hire service in this case claims to power attacks in excess of 3.5 Tbps, which is about half of the bandwidth of a cyberattack that Cloudflare last year called the “largest DDoS attack ever recorded.”
For years, authorities such as the FBI and Europol have played a game of whack-a-mole against these services, taking down and seizing domains, and sometimes arresting the people behind them.
This story was updated to include Canonical’s response.