U.S. officials say they have seized dozens of domains linked to some of the world’s leading distributed-denial-of-service-for-hire websites. But TechCrunch found that several of the seized sites are still online.
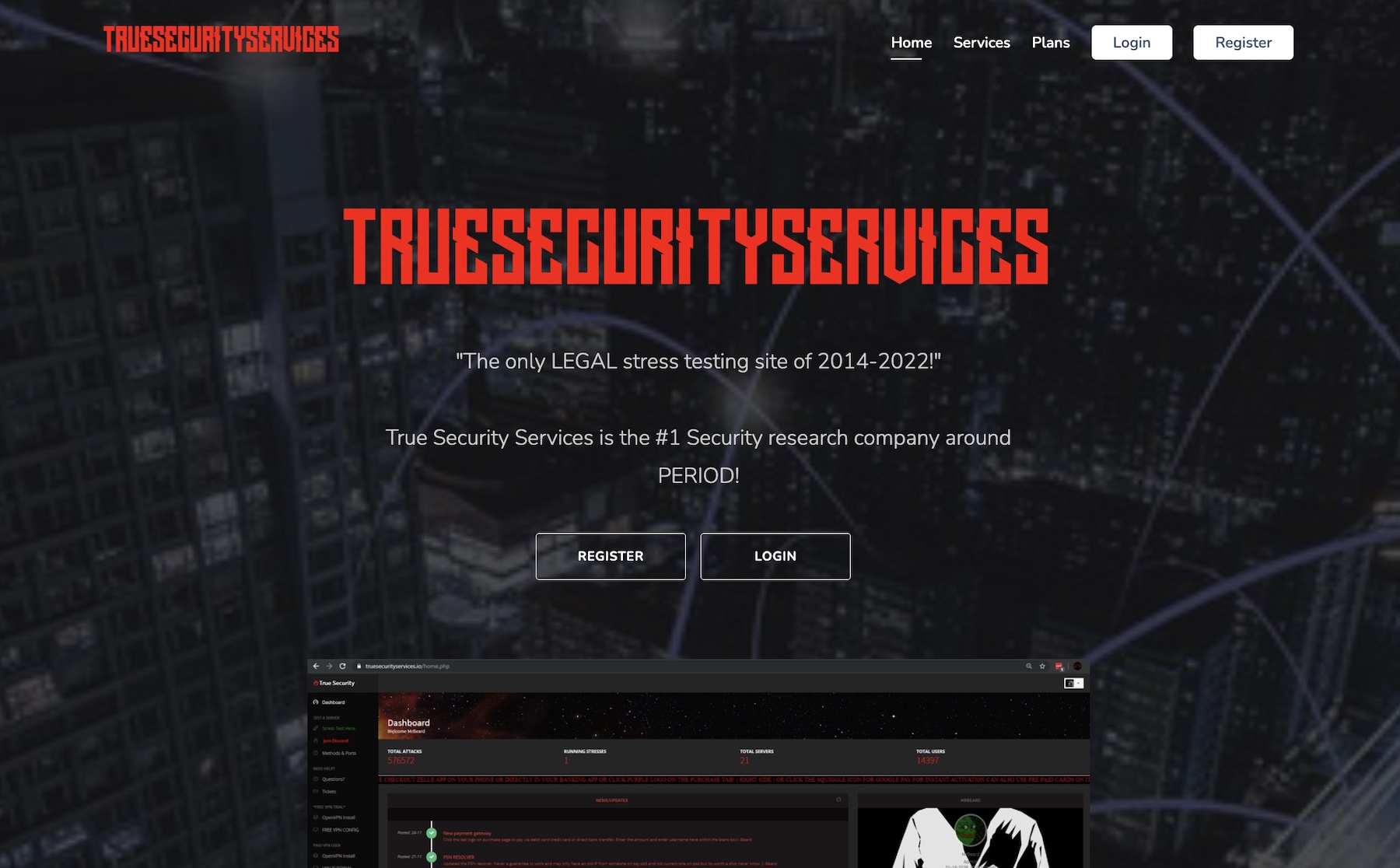
In a press release on Wednesday, the U.S. Department of Justice announced the takedown of 48 domains associated with some of the world’s most popular DDoS booter platforms, according to the corresponding warrant. These services, often marketed as sites for bandwidth stress-testing networks, allow low-skilled individuals to carry out DDoS attacks designed to overwhelm websites and networks and force them offline.
The takedowns were carried out as part of a joint operation between the U.K.’s National Crime Agency, Dutch police and Europol, known as “Operation PowerOFF.”
The DOJ said these booter sites were involved in attacks against a wide array of victims in the U.S. and abroad, including educational institutions, government agencies and gaming platforms. Europol notes that one of the sites seized has been used to carry out more than 30 million attacks.
While many of the websites targeted by the operation now display a message stating they have been seized by the FBI, TechCrunch found that — at the time of writing — at least eight of the sites supposedly seized by U.S. prosecutors continue to load as normal. It’s unclear why these sites continue to load.
Operation PowerOff also saw law enforcement officials arrest seven individuals who allegedly oversaw the DDoS booter services. In the U.S., criminal charges have been filed against six individuals: John M. Dobbs, Jeremiah Sam Evans, Angel Manuel Colon Jr., Shamar Shattock, Cory Anthony Palmer and Joshua Laing.
At the time of writing, the DDoS-for-hire service allegedly run by Laing remains online.
Disrupt 2026: The tech ecosystem, all in one room
Your next round. Your next hire. Your next breakout opportunity. Find it at TechCrunch Disrupt 2026, where 10,000+ founders, investors, and tech leaders gather for three days of 250+ tactical sessions, powerful introductions, and market-defining innovation. Register now to save up to $400.
Save up to $300 or 30% to TechCrunch Founder Summit
1,000+ founders and investors come together at TechCrunch Founder Summit 2026 for a full day focused on growth, execution, and real-world scaling. Learn from founders and investors who have shaped the industry. Connect with peers navigating similar growth stages. Walk away with tactics you can apply immediately
Offer ends March 13.
DOJ spokesperson Thom Mrozek told TechCrunch that there was a delay in getting the FBI splash-pages. “We are working with the registries to make this happen.” Mrozek said while some sites remain online, the sites are “no longer functioning” and cannot be used to launch attacks.
The U.K.’s NCA announced that it has also arrested an 18-year-old man in Devon, who is suspected of being an administrator of one of the seized sites. The NCA added that customer data from all of the DDoS booter sites was obtained and will be analyzed by law enforcement.
“Admins and users based in the UK will be visited by the National Crime Agency or police in the coming months,” the NCA warned.
Updated with remarks from the Justice Department.
FBI kicks some of the worst ‘DDoS for hire’ sites off the internet


