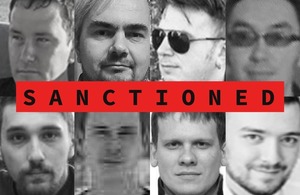
U.S. and U.K. authorities have sanctioned more alleged members of the notorious Russia-based Trickbot cybercrime gang.
The U.S. Treasury and U.K.’s Foreign Office announced on Thursday fresh sanctions against 11 individuals “involved in management and procurement for the Trickbot group.” This comes just shortly after the two nations imposed sanctions against seven leading members of Trickbot in February.
The Treasury said that the U.S. Department of Justice is concurrently unsealing indictments against nine individuals in connection with the Trickbot malware and Conti ransomware schemes, including seven of the individuals designated today.
These individuals, which the authorities have linked to Russian intelligence services, include Andrey Zhuykov, Maksim Galochkin, Maksim Rudenskiy, Mikhail Tsarev, Dmitry Putilin, Maksim Khaliullin, Sergey Loguntso, Alexander Mozhaev, Vadym Valiakhmetov, Artem Kurov and Mikhail Chernov.
“The targets designated today include administrators, managers, developers, and coders who have materially assisted the Trickbot group in its operations,” said the U.S. Treasury. Two of the individuals were allegedly tasked with overseeing the gang’s human resources functions, according to the announcement.
One of these individuals, Maksim Galochkin, was last week identified as a central figure of the Trickbot gang following a months-long Wired investigation, though it’s not known if the publication’s investigation sped up today’s announcement. As reported by Wired, Galochkin — known online as “Bentley” or “Manuel” — led a group of testers, with responsibilities for development, supervision and implementation of tests for the Trickbot group, according to the Treasury.
The U.K.’s National Crime Agency said in today’s announcement that Trickbot is responsible for extorting at least $180 million from victims globally and has extorted at least £27 million ($33.6 million) from 149 U.K.-based victims, a list which includes hospitals, schools, local authorities and businesses.
Disrupt 2026: The tech ecosystem, all in one room
Your next round. Your next hire. Your next breakout opportunity. Find it at TechCrunch Disrupt 2026, where 10,000+ founders, investors, and tech leaders gather for three days of 250+ tactical sessions, powerful introductions, and market-defining innovation. Register now to save up to $400.
Save up to $300 or 30% to TechCrunch Founder Summit
1,000+ founders and investors come together at TechCrunch Founder Summit 2026 for a full day focused on growth, execution, and real-world scaling. Learn from founders and investors who have shaped the industry. Connect with peers navigating similar growth stages. Walk away with tactics you can apply immediately
Offer ends March 13.
The group has also targeted a number of U.S. organizations, including U.S. government entities, according to the Treasury.
Trickbot, which first emerged as a banking trojan in 2016, was previously linked to a 2021 ransomware attack on the Los Angeles Unified School District, or LAUSD — the second largest district in the U.S. The gang also deployed ransomware targeting three medical facilities in Minnesota, according to the U.S. Treasury, resulting in the diversion of ambulances.
The sanctions, while largely symbolic since Russians are shielded from extraditions by the Kremlin, mean the 11 individuals have had their assets frozen, travel bans imposed and are barred from transacting with organizations in the U.K. and the U.S., which themselves face action if they engage with the sanctioned individuals. This will make it harder for the hackers to launder money associated with their criminal activities.
US, UK sanction 7 alleged members of infamous Russian Trickbot hacking gang


